What is Computer Security | Common Computer Security Threats

Read on to get detailed knowledge about computer security, safety risks, and how to protect your computer.
Your computer plays hide and seek with numerous security threats each day. What we mean is a lot of dangers constantly endeavor to find and attack your device. Whenever you use the internet, download new software, import a file, or perform other tasks, it becomes easier for hackers, viruses, and other issues to catch your machine.
After entering the device, the common computer security threats may make you face a lot of hardships.
For instance, they may steal your data and extort money in return for it, use your personal information for fraudulent purposes, and cause many other problems.
Hence, it is essential to learn about the most common computer security threats and how to protect yourself from them.
This article talks about various aspects related to computer cyber security and associated threats in detail. But before moving any further, let’s first discuss what computer security is to give you a better understanding of it.
Introduction to Computer Security
If we talk about the basic definition of computer security, it is to protect your device and information from unauthorized use, damages, and theft.
In other words, the meaning of computer security is a set of systems for protecting your computer from all things that may be potentially harmful to the device and your privacy.
Some examples of computer security include two-way authentication, password protection, etc. We are going to learn more about these mechanisms to keep the computer secure later in this article.
Before proceeding further, it is crucial to discuss the types of computer security so that you can secure yourself from threats (mentioned in the coming sections) better.
Also Read: Critical Security Flaws Found in Popular VPN Apps
Types of Computer Security Systems
Now that you have learned what computer safety is, you should also note that it may take various forms. The types of security depend upon what you want to protect on your computer. Generally, computer security may be of the following types.
Application Security
Since apps on your computer are a soft target for attackers, you can protect them with application security. It adds security features to the apps to keep them safe from cyber-attacks.
Web application firewalls, antivirus software, firewalls, passwords, and encryption are a few examples of application security systems.
Information Security
If you are worried about the unauthorized use of your computer system or breach of its confidentiality, availability, and integrity, you may employ information security. This type of computer security focuses on protecting information through the CIA triad model that makes sure that data remains secure at all times without loss of productivity.
Network Security
Cybercriminals are often on the lookout for loopholes in the network to invade your computer. Therefore, you must have a network security mechanism in place to prevent unauthorized access to your computer networks.
Endpoint Security
The responsibility of protection from computer threats always rests with the end-user. However, many times, users unintentionally help attackers fulfill their unlawful purposes (for example, users often click on malicious links unknowingly).
Therefore, endpoint security aims to create awareness among users about computer security topics, such as phishing/social engineering attacks, creation and usage of passwords, device/physical security, and the importance of cybersecurity.
Internet Security
As you may already know, the internet is a virtual door to a lot of things, such as information and computer safety risks (like viruses, spyware, and other malware). Therefore, internet security means protecting the computer from various internet-based issues.
Above, we have discussed computer security’s definition and its types to give you a basic idea of the topic. Now, in our view, you are well prepared to combat the following personal computer threats that you may encounter.
Most Common Computer Security Threats
Now, it’s time to know the computer security risks that may come your way. We share them below.
1. Phishing
Phishing attacks are common and one of the most potential threats to computer security. According to recent research, over 81% of organizations fell prey to phishing in the past year.
Most commonly, phishing attacks occur through emails. The attacker uses a familiar-looking email address to trick you. If you click on the mail, open the given attachment, and fill in the required information, you end up losing your data. Moreover, users even reported financial losses due to computer security threats like phishing.
Apart from emails, hackers have also started phishing through the cloud applications of companies. Therefore, you should take appropriate steps to protect them.
2. Malware
If you get an error message “Serious security threats have been detected on your computer”, your device might be malware-infected. Malware is malicious software, like spyware, ransomware, viruses, etc. Malware attacks happen when you click on any infectious link or email attachment.
Once inside your computer, malware can cause a lot of damage, such as the installation of harmful software, preventing access to the network’s key components, gathering your private information, and more.
Note: According to a recent study, ransomware attacks saw an increase of over 140% in 2021’s third quarter alone. Going by the numbers, you can estimate that there might be an exponential increase in malware attacks in 2022.
Also Read: Best Free Malware Removal Tools for Windows
3. Man in the Middle
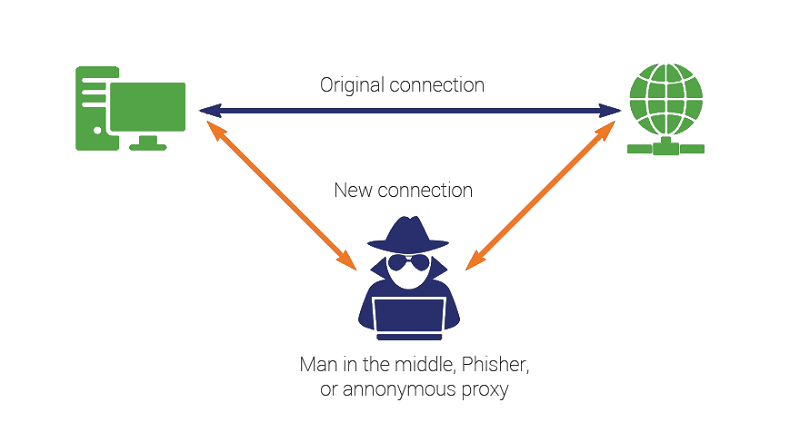
MitM or Man in the Middle is one of the types of computer threats where the hacker places himself between a two-party transaction. Once the cybercriminal enters the communication, he may steal sensitive data.
Man in the Middle attacks mostly occurs through unsecured public WiFi networks. Hence, you must use them cautiously.
4. Denial of service
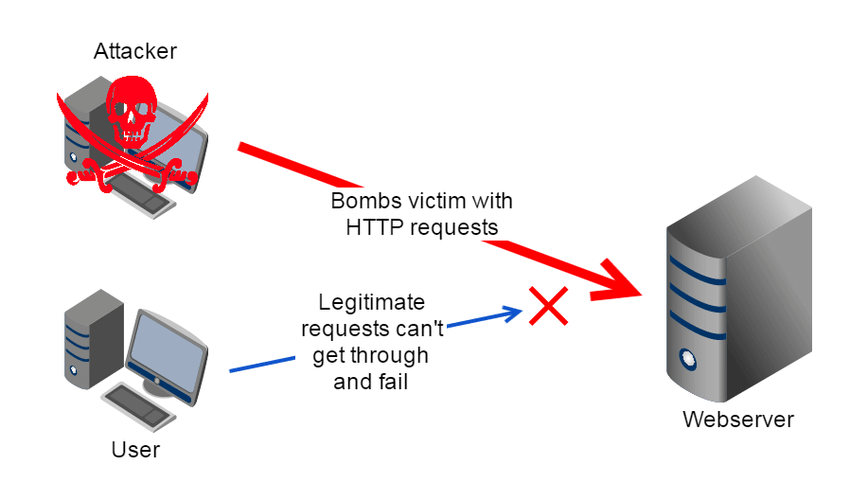
Another threat to computer cyber security is the denial of service attacks. These kinds of attacks prevent you from accessing the machine or network resources. It floods the system, network, or servers with useless data and requests to make them inaccessible.
Moreover, through distributed denial of service, attackers can even attack your device using many infected devices.
Note: According to the recent figures, denial of service attacks cost over $20000-$40000 per hour to a company. That’s quite a huge amount!
5. SQL Injection
The next computer security risk you may face is SQL injection. Here, cybercriminals insert malicious code into SQL servers to access the database. After accessing the server, the attacker can view the data, change, or delete it.
6. Emotet
Let’s now talk about Emotet. It is a Trojan (type of malware) that enters your computer to steal your sensitive or confidential information.
Emotet makes its way to your computer through spam emails, malicious scripts, or infected links. It is regarded as one of the most expensive and harmful malware.
Note: Emotet does not stay on a single computer. It replicates itself like a worm and spreads the infection to all connected computers. According to recent statistics, Emotet has already affected more than 5% of organizations across the globe.
7. Social engineering attacks
Perhaps the most common form of protection from unauthorized use of a computer system is the password. However, with the rise of social engineering attacks, even passwords are at risk.
Hackers use social engineering or a strategy involving human interactions to trick users into revealing their passwords. Moreover, other forms of social engineering attacks include accessing the security keys (passwords) through guessing or a password database.
Note: According to recent research, social engineering attacks increased by an alarming rate of 270% in the year 2021 and are expected to rise even more in 2022.
Also Read: Android Malware ‘Unkillable’ Gives Hackers Full Remote Acces
8. Zero-day exploit
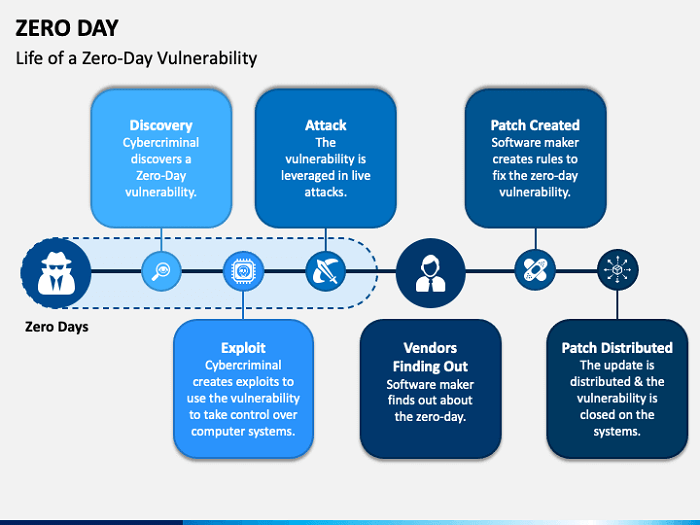
No software or application is foolproof. Almost all programs have certain vulnerabilities that may pave the way for hackers to invade your system. Zero-day exploits happen when these loopholes become known to notorious minds before the software/app developers release a patch update to fix them.
Note: As witnessed by researchers, zero-day exploits increased dramatically by 100% from the year 2020 to 2021. These attacks are on a rise in 2022 as well.
9. Advanced persistent attacks
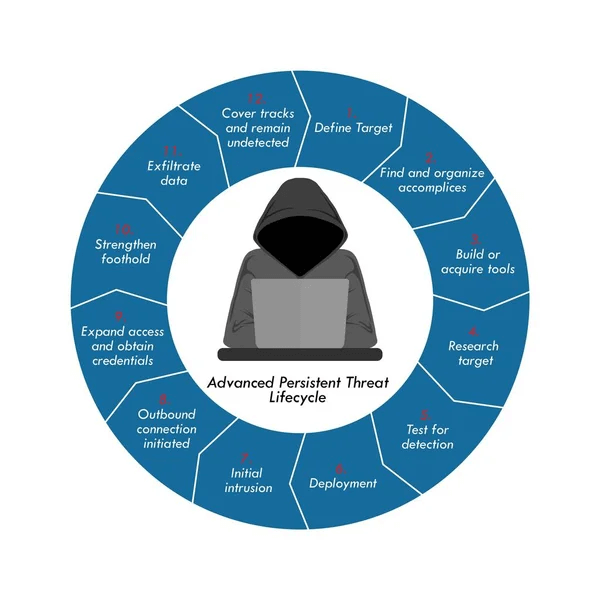
When a malicious actor enters a network or system and remains undetected for a significant period, we call it an advanced persistent attack. Here, the attacker aims to keep a check on your network activity to gain crucial information about the target.
The target of advanced persistent attacks is mostly esteemed enterprises, national sites, and other high-value victims.
Note: Various researches predicted that in 2022 mobile devices, supply chains, and cloud computing software will be among the top victims of advanced persistent attacks.
10. IoT attacks
In the modern world, IoT (Internet of Things) has gained immense popularity. Cybercriminals attack IoT devices through botnets. The botnet malware looks for unguarded devices on the internet and infects as many devices as it can.
The botnet uses the power and resources of the infected devices for various automatic activities that are unknown to the device user. Moreover, hackers employ these botnets to execute email spamming, fraudulent campaigns, malicious traffic generation, and other unlawful activities.
Note: As reported by Gartner, over 25% of cyberattacks will relate to IoT in the time to come.
After learning about the most common computer security threats, you might be wondering how to protect your device from them, right? Well, we share the same in the next section.
How to Protect the Computer from Security Threats
You can follow some simple tips to safeguard your computer and data. They are given below.
Use strong passwords
Passwords are the most common tool to protect your computer and data from unauthorized access. You must keep a password that is hard enough to guess. You may use a combination of numbers, letters, and symbols to create such a password.
Install an antivirus software
Antivirus software is the protective shield you need to safeguard your data from the prying eyes of hackers. It helps keep away viruses and other malware. It also lets you detect and remove viruses with ease if ever your device gets infected. If you are confused about which antivirus to use, you may pick one of our top recommendations.
Update your operating system, applications, and browser
Updates patch the security loopholes that hackers may exploit for their unlawful purposes. Moreover, the first rule of computer security is to check patches. Hence, we always advise our readers to keep their OS, Web browser, and applications up-to-date at all times.
Ignore suspicious looking emails
Hackers often use lucrative emails to deceive the target. Thus, if an email looks too good to be true, never click on it. For example, if you get an email that says you won a one million dollars lottery, that’s most likely a scam designed to rob you. Hence, resist the temptation to claim the reward.
Employ two-factor authentication
Passwords are the most common method of authentication. However, as hackers have now become intelligent enough to crack weak passwords, many websites provide an option of two-factor authentication. Here, you get access after entering your password and another form of verification, such as an OTP (One Time Password) received on your email/mobile number. We find it better to keep the two-factor authentication and recommend doing the same to our readers.
Above, were the security threats to your computer and ways to keep them at bay. If you still have any questions or confusion, you can go through the next section to find the needed answers.
Also Read: Best Free Spyware Removal Tools For Windows PC
Frequently Asked Questions
Below we answer all questions about computer cyber security that may linger on your mind.
Q1. What is data security?
In simple terms, data security is one aspect of information technology that is concerned with protecting software and data from unauthorized tampering or damage.
Q2. What is computer privacy?
Simply put, computer privacy is your ability to decide what data on your computer can be communicated with third parties. No information can be shared with any third party without your knowledge.
Q3. What is a computer security risk?
All things that may damage your data or allow any unauthorized access to it is known as a computer security risk. Anything can result in computer safety risks, including viruses, ransomware, and other malware.
Q4. What is the importance of computer security?
Data protection is the prime importance of computer safety. Apart from this, below are other factors that make computer security important.
- Protection of organization properties
- Prevention of viruses and other malware
- Minimizing the risk of unauthorized access
Q5. Which factor causes most problems associated with computer security?
Accidental errors are the element that results in a lot of problems related to computer security.
Q6. Which is an example of a lack of computer security?
Spam is the most common example of not having enough computer security. Whenever you have a lot of spam emails or messages, there may be something wrong with your security system.
Q7. Which type of privacy law affects computer security?
Any privacy law applicable to your organization affects computer security. For example, if COPPA (Children’s Online Privacy Protection Act) applies to your organization, it impacts your computer security.
That’s All for Computer Security and Associated Threats
In this article, we looked at various computer security threats and solutions. We hope this write-up helped you understand the most common computer safety risks and how to keep them away from your device.
The modern-day world has a lot of open gates for hackers and cybercriminals to invade your computer. Thus, we advise you to remain vigilant at all times.
If you have any questions or concerns about this article, we are happy to address all your queries. Feel free to drop us a comment.


